Privacy plan: The next space of concern is a VPN’s privacy coverage.
This document tells you what sort of knowledge the company collects and what specifically they do with it. All VPNs require to obtain some details if only to bill you and keep a high-quality services, so you shouldn’t be alarmed if a corporation has your credit score card quantity or your electronic mail address. Even so, less than no situations must a VPN log your IP tackle, your browsing behaviors, or any other information related to your time in the VPN tunnel.
Place: Lastly, you should usually examine out in which your VPN is headquartered. If a enterprise is found in a single of the 5 Eyes, Nine Eyes, or fourteen Eyes nations, government businesses and regulation enforcement can subpoena the company’s customer details. There are, nonetheless, exceptions to this basic rule.
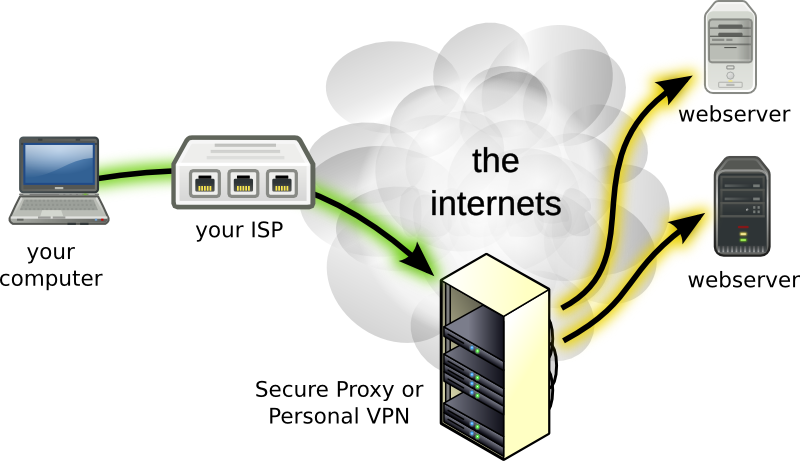
A organization in the U. S. with a coverage that states they don’t log IP addresses, time stamps, or on the net activity, for case in point, is not going to have everything helpful to switch around need to the govt subpoena them. How Does a VPN Perform?A VPN is an encrypted tunnel as a result of which you hook up to the world-wide-web. While your data is in the tunnel, your IP tackle and on-line routines must be fully hidden from many others.
Typically, you log on to your chosen VPN as a result of an application or a consumer mounted on your product. Most VPNs retain hundreds or even countless numbers of servers positioned in nations close to the world. When you log on vpn for online gambling to the VPN, you hook up to a unique server, and that server concerns an IP tackle which masks your genuine IP handle. Almost everything you do in the VPN tunnel is attached to that nameless tackle. Furthermore, the VPN tunnel by itself hides all of your activity beneath a layer of encryption protocols so that even if another person ended up able to see that exercise, they’d be unable to decode it. What Is Encryption?In the easiest phrases, encryption indicates encoding facts, and it truly is a procedure for concealing info that dates back hundreds of years. Simultaneous encryption, the basis for most of today’s VPN encryption, essentially dates back some 2,five hundred years to the Greeks’ Caesar cipher.
VPN encryption is created on this process, but it takes advantage of considerably additional advanced encoding approaches than Caesar could have dreamed of, these as:AES encryption: The complexity of the encoding cipher decides how tough the code is to crack. The existing regular in ciphers is AES encryption. Created for use by the U. S.
military services in the early 2000s, AES will involve separating textual content into a collection of grids and then scrambling the grids. AES divides info streams into 128-little bit chains of cipher blocks. The “critical” to deciphering these chains can be 128, 192, or 256 bits very long, each individual progressively tougher to split.
Public crucial encryption: The risk with symmetric encryption is that another person will discover the vital to the cipher. This important is especially susceptible when a person side sends it to the other. Public key encryption solves this issue by making use of individual encryption and decryption keys.
The VPN server uses a publicly available important. The user, nevertheless, has their own private key for decrypting the details. Transportation layer security: VPNs use transportation layer safety (TLS) to authenticate both equally sides of the VPN connection. TLS makes certain that a hacker or spy are unable to faux to be the consumer or the server in purchase to steal the vital. Commonly, a VPN employs TLS encryption when a consumer first connects. What Are Protocols?Internet protocols are the guidelines a VPN follows for transmitting details across its community.